In Part 1 of this blog series, we have seen how the attack potential of an attacking agent can be modeled. For our system, we also want to model the parts and aspects that we want to protect and the damage that can be done by an attacker. So as a next step, we will model damage classes and damage potential.
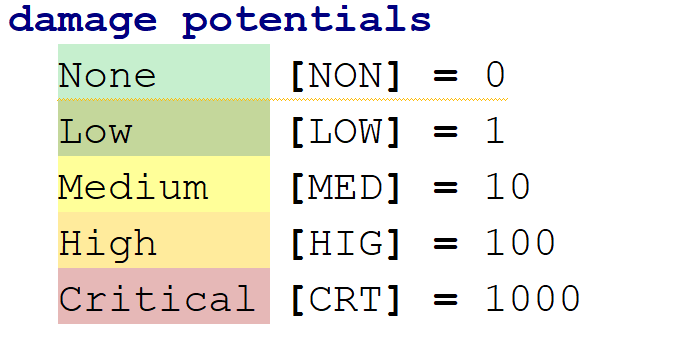
Damage Potential
Damage potential is a categorization of the damage that could be done to the system. It maps damage potential values to numerical values. These values are then later used in calculations of combined and derived damage potentials. The list of damage potentials and their values can be defined freely according to the security analysis method that is being used.
![]()
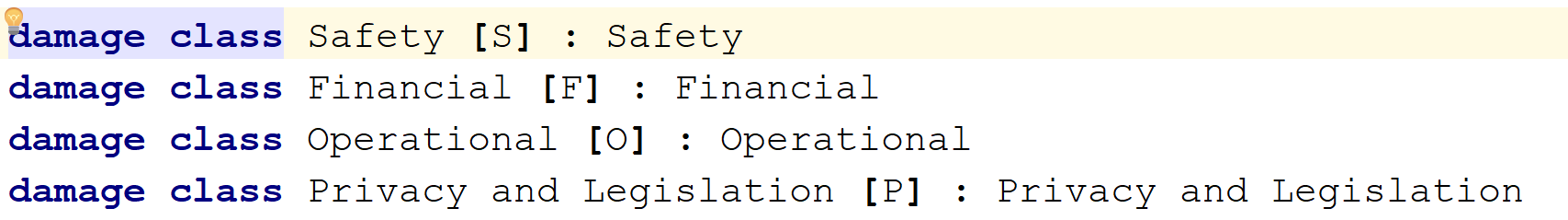
Damage Classes
The kind of damage that can be done do the system can be categorized into classes and then further refined. In our example we have the following coarse classes:
![]() In a further step, these classes are refined into subclasses and assigned damage potential values (example given for the Safety class):
In a further step, these classes are refined into subclasses and assigned damage potential values (example given for the Safety class):
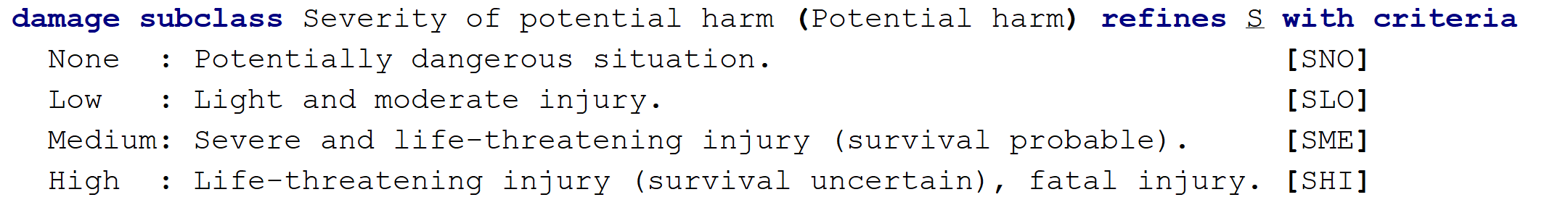
Note that the first column of the table contains the damage potential that is assigned to each subclass.
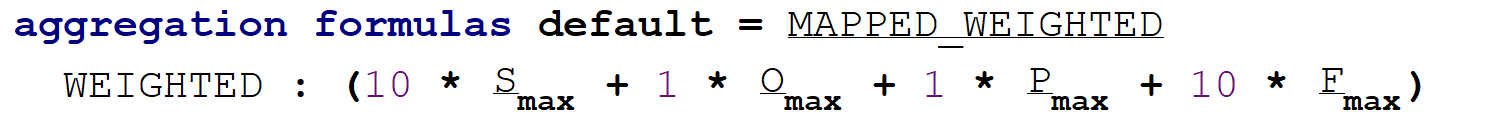
Combining damage classes
In some calculations, we might encounter a combination of damage classes and we want to be able to prioritize damage classes over each other. So we can freely define formulas that are to be used in the system to calculate combinations. In this case, we consider safety and financial damage to be 10 times more important than other damage:
Preview: Security Goals
We now have almost all building blocks to describe security goals, which will be the content of the next part of this series. Note the following example:
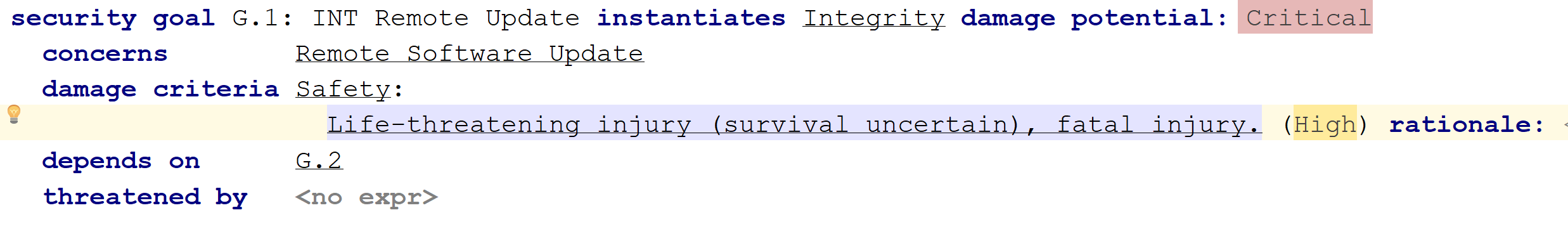
The damage assigned to this criteria is Safety, whith a subclass that has a "high" damage potential. But the overall damage potential of the security goal is calculated by applying the formula, i.e. multiplying the safety value by 10, resulting in a critical damage potential.

Comments